Key takeaways
- In early April 2026, attackers compromised updates for 30+ popular WordPress plugins, plus a separate compromise of Smart Slider 3 Pro. The payload served SEO spam only to Googlebot, which can silently destroy organic rankings.
- Webserv audited every WordPress site on the client roster against the published affected-plugin list and escalated findings directly to each client.
- We built a custom Claude AI skill that plugs into Wordfence’s public vulnerability API and scans every client WordPress site weekly, so a new CVE is flagged and brought to the client’s attention within days instead of weeks.
A different kind of WordPress attack
Between April 5 and April 7, 2026, attackers gained control of the update infrastructure for 30+ WordPress plugins, many of which were sold under the “Essential Plugin” umbrella. A parallel compromise hit Smart Slider 3 Pro. For a short window, anyone who pressed “Update” on an affected plugin had the attacker’s version installed via the official update channel.
What made this one different from a typical plugin vulnerability was the payload. It wasn’t defacement. It wasn’t ransomware. It was SEO spam, shown only to Googlebot.
Here’s the trick:
- Site owners don’t see it. When you visit your own site, everything looks normal.
- Google sees it. Googlebot gets served hidden links to pharma, casino, loan, and other spam content.
- Rankings collapse. Google assumes your site is trying to manipulate search results and silently penalizes it.
Think of it as digital graffiti that only Google can see. For any business that depends on organic search, and for our behavioral health clients that’s almost all of them, this attack can do real damage before anyone realizes something is wrong.For the full technical breakdown, Anchor Hosting published an excellent post-mortem: Someone Bought 30 WordPress Plugins and Planted a Backdoor in All of Them.
Why SEO-driven businesses are the real target
Most WordPress vulnerabilities hit predictable surfaces like contact forms, login pages, and file uploads. You fix them, you move on.
Supply-chain attacks like this one are different:
- The malicious code arrives through the official update process. Every piece of security hygiene we tell clients to follow (“keep plugins updated”) actually delivered the payload in this case.
- The damage shows up as SEO loss, not a site outage. Traffic and rankings decline quietly over weeks. By the time anyone notices, recovery can take months.
- There’s a 30-day lag baked into most defenses. Free security tools typically update their rules on a 30-day delay. These attacks do their damage in the first 24 to 72 hours after disclosure.
That 30-day gap is exactly where SEO-sensitive sites get hit.
How Webserv responded
When this landed, my first message to the internal response team was blunt:
“Hey, starting this channel as we need to get ahead of this malware thing as much as we can. I was able to use the free Wordfence API to help us scout for vulnerabilities in our clients’ sites. We need to prioritize looking at all of these.”
Here’s what we did in the week that followed.
1. Audited every WordPress client site against the affected plugin list
We checked every site on the Webserv roster against the complete published list of 30+ compromised plugins, including the Essential Plugin set and Smart Slider 3 Pro.
2. Escalated findings directly to every client
Whether a client was in the clear, potentially affected, or carrying an unrelated high-severity CVE we surfaced during the sweep, we emailed each one directly with a plain-English explanation: what we checked, what we found, and what we’d recommend as next steps.
I was direct with the account managers about the urgency:
“Ideally, even for sites you don’t get to today, send it today and say you’re prioritizing it.”
When something like this hits, transparency matters more than polish.
3. Installed Wordfence free as a baseline protection layer
We installed the free version of Wordfence on every WordPress client site that didn’t already have it. This adds a firewall and basic malware scanning as a baseline. It’s a lightweight first line of defense, and it’s now standard across every Webserv-managed WordPress site.
4. Recommended the right specialist path for cleanup
For any site that needed deep remediation, we pointed clients at Wordfence’s Care or Response tier, which is built for exactly this work. We’re not a cybersecurity firm, and the honest thing to do when something falls outside our scope is to recommend the people who specialize in it.
What we’re doing going forward
This is the part we want to be specific about because trust depends on clarity of scope.
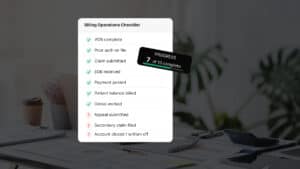
What we are doing, every week, for every WordPress client site on our roster:
- Scanning. Our custom Claude automation I built pulls the current CVE feed from Wordfence’s public API and cross-matches it against the plugins installed on every client site.
- Triaging. Findings are ranked by CVSS severity (P0 supply-chain compromises, P1 critical CVEs, P2 high and medium backlog, P3 possibly vulnerable).
- Flagging. Anything material gets surfaced to the client’s account manager within days of disclosure, and the AM passes it on to the client with clear context.
- Advising. We explain what the vulnerability is, why it matters for SEO specifically, and what the recommended path forward is (patch, replace, remove, engage a specialist).
Our role is to surface issues that could hurt your search rankings, bring them to your attention quickly, and point you at the right resources to fix them.
How our weekly WordPress vulnerability scan works
We want to be transparent about the tooling, because we think it matters (also, this stuff is really fun to build).
Our weekly scan is a custom internal automation we built using Anthropic’s Claude, which plugs directly into Wordfence’s free public vulnerability API. Here’s what it does, end to end:
- Fingerprints each client site. For every WordPress site on our roster, it identifies the installed plugins and their version numbers externally, just as an attacker would conduct reconnaissance on a site. No credentials required.
- Pulls the current CVE feed from Wordfence. Same feed that powers Wordfence’s paid products, made freely available via their API for exactly this kind of use.
- Cross-matches the two. Every plugin on every client site is checked against every known CVE. If a version is vulnerable, it gets flagged.
- Ranks by severity. Results are sorted by CVSS score (the industry-standard 0 to 10 severity rating).
- Delivers a weekly report to our internal response channel with a per-client priority list: P0 supply-chain compromises, P1 critical CVEs, P2 high and medium backlog items, and P3 possibly-vulnerable sites that need a manual admin-side check.
From there, your AM picks it up and brings the relevant findings to you.
A few honest notes:
- It is not a replacement for a dedicated security product. It’s a monitoring layer that lives on top of tools like Wordfence.
- We built it because the alternative was slower. Before this, catching a new CVE relevant to a specific client meant someone reading a security newsletter, cross-referencing a spreadsheet, and pinging the right AM. The April incident showed us that “someone catches it eventually” is not a viable protocol when SEO damage starts within 72 hours of disclosure.
- AI made it possible for a small team. Building and running a portfolio-wide vulnerability scanner used to require dedicated engineering time, which we don’t have as an SEO agency. Using Claude to build it meant we could ship in days instead of quarters, and we think that’s a reasonable thing to be open about.
If you want to know whether a specific finding on your site came from our scan, or you have questions about how it works, ask your Webserv AM. We’re happy to walk through it.
Why we recommend Wordfence
For ongoing protection, we recommendWordfence, specifically the Premium tier (around $149 per year per site).
The free version we’ve installed on every client site covers the basics. Premium adds two things that matter a lot for SEO-sensitive businesses:
- Real-time firewall protection. Premium rules update the moment a vulnerability is publicly disclosed, not on a 30-day delay. Given that attacks like the April one do their damage in the first 24 to 72 hours, that delta is where sites actually get protected.
- Real-time malware signatures. Same principle, but for malware already living on a site rather than active attack attempts.
If a site is ever actively compromised and needs forensic cleanup, Wordfence’s Care or Response tiers include that work directly. For any business where organic search drives inquiries and revenue, that package is a cheap insurance policy against something that’s genuinely hard to recover from.
FAQ: The April 2026 WordPress plugin attack
Was my site affected?
If you’re a Webserv client, your account manager has already emailed you with site-specific findings: what we audited, what was present, and what we’d recommend as next steps. If you haven’t seen that email, reach out to your AM or message us at olivia@webserv.io.
How do I check whether a non-Webserv site is affected?
Three quick self-checks:
1. Compare your installed plugin list against the published affected list from Anchor Hosting.
2. Open Google Search Console and look for unusual query impressions. Pharma, casino, loan, or Japanese-language queries showing up for an English-language site are classic tells.
3. Check the file size of your wp-config.php. A clean version is typically around 3 to 5 KB. The compromised version is around 9 KB or larger.
Do I need Wordfence Premium, or is the free version enough?
The free version is a reasonable baseline for personal blogs and low-stakes sites. For any business where organic search drives revenue, the 30-day rule-update gap in the free tier is a real risk. Premium’s real-time firewall closes that gap.
What if we already use a different security provider?
That works too. The main thing is having a clear path for both ongoing protection and forensic cleanup if something ever hits. Tell us what you’re using and we’ll make sure our scan findings are delivered in a format that fits your provider’s workflow.
Does Webserv manage our WordPress plugins for us?
No. Plugin management and patching sits with your dev team (or your hosting provider, or a cybersecurity partner). Our role is to scan weekly, flag anything that could hurt your SEO, and bring it to your attention with recommended next steps.
How often will Webserv scan my site going forward?
Weekly, automatically, for as long as you’re a Webserv WordPress client. You don’t need to do anything to opt in.
If your rankings dropped in April, investigate
This attack was quiet. The next one will be too.
If you’re a Webserv client, our weekly scan is now running in the background and we’ll proactively flag anything that affects you. If you’re not a Webserv client and your organic traffic took an unexplained hit in April, it’s worth running the three self-checks above. Recovery from SEO-targeted malware is much faster when you catch it early.
Questions about this post, your own site, or how our weekly Wordfence scan works? Get in touch. I’d love to help you out.